Data breaches climbed to a record high in 2025. How to protect your personal information
Data Breaches Climbed to a Record High in 2025: How to Protect Your Personal Information Now
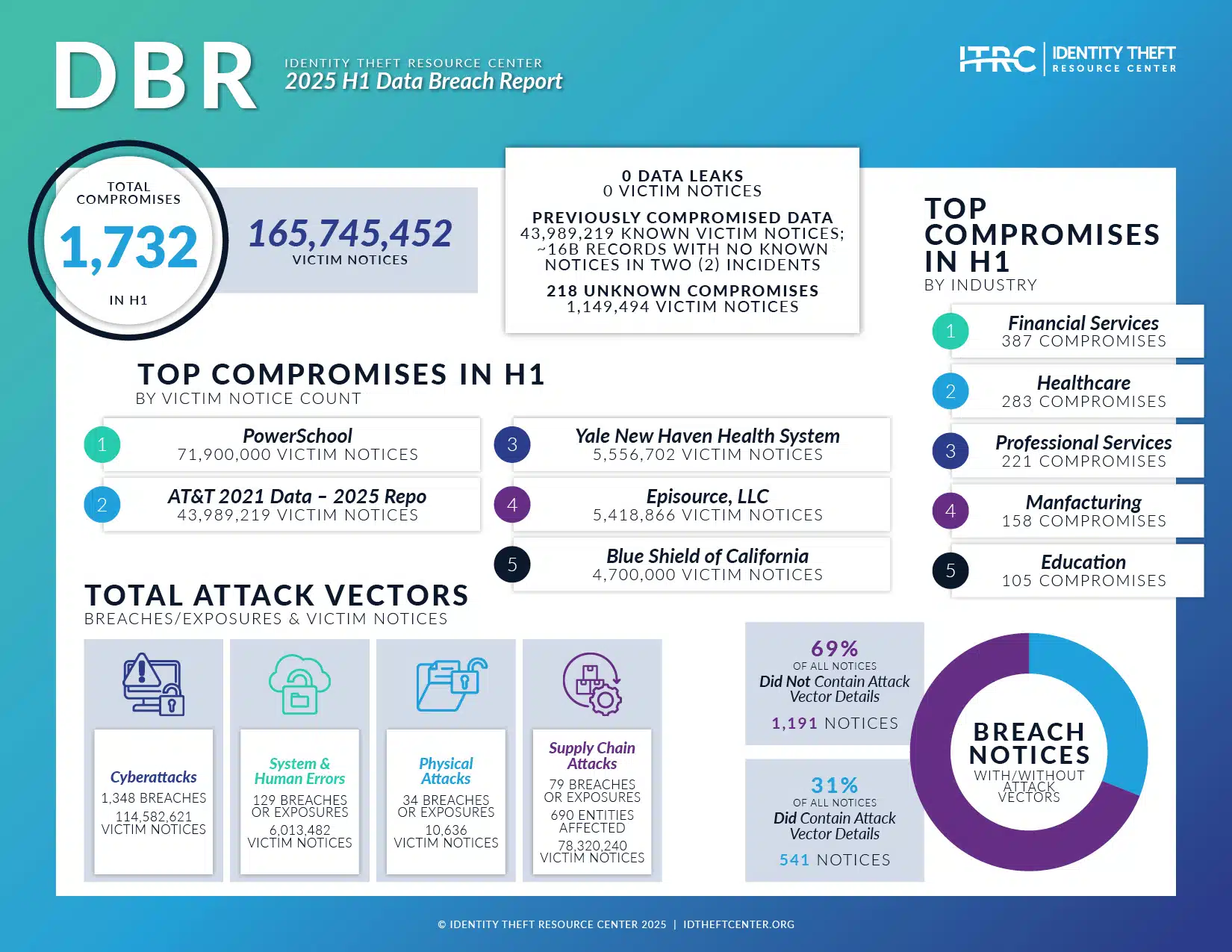
The mid-year statistics for 2025 have confirmed the worst fears of the cybersecurity world: data breaches are escalating at an unprecedented rate. Reports indicate that both the frequency and severity of compromises have surged past previous records, affecting millions of users globally. This isn't just a corporate problem anymore; it is a crisis of personal security.
The sheer volume of exposed records—spanning financial data, health records, and deeply personal communications—means that virtually every connected user has a growing exposure risk. The convenience of the digital age is now coupled with the constant threat of sophisticated cybercriminals.
Consider the case of Maria L., a marketing executive in New York. Her bank account was drained after a major retail chain she shopped at suffered a massive breach in February. "I thought I was safe because I used a complex password," she explained. "But the breach exposed the security questions I used everywhere—my mother's maiden name, my first pet. They had enough information to reset my bank password and transfer everything out within 48 hours. The damage caused by identity theft is truly devastating." Maria's experience underscores a critical truth: traditional defenses are failing. To survive the 2025 breach epidemic, you must fundamentally change how you safeguard your digital life.
Understanding the Cyber Threat Landscape That Led to the 2025 Spike
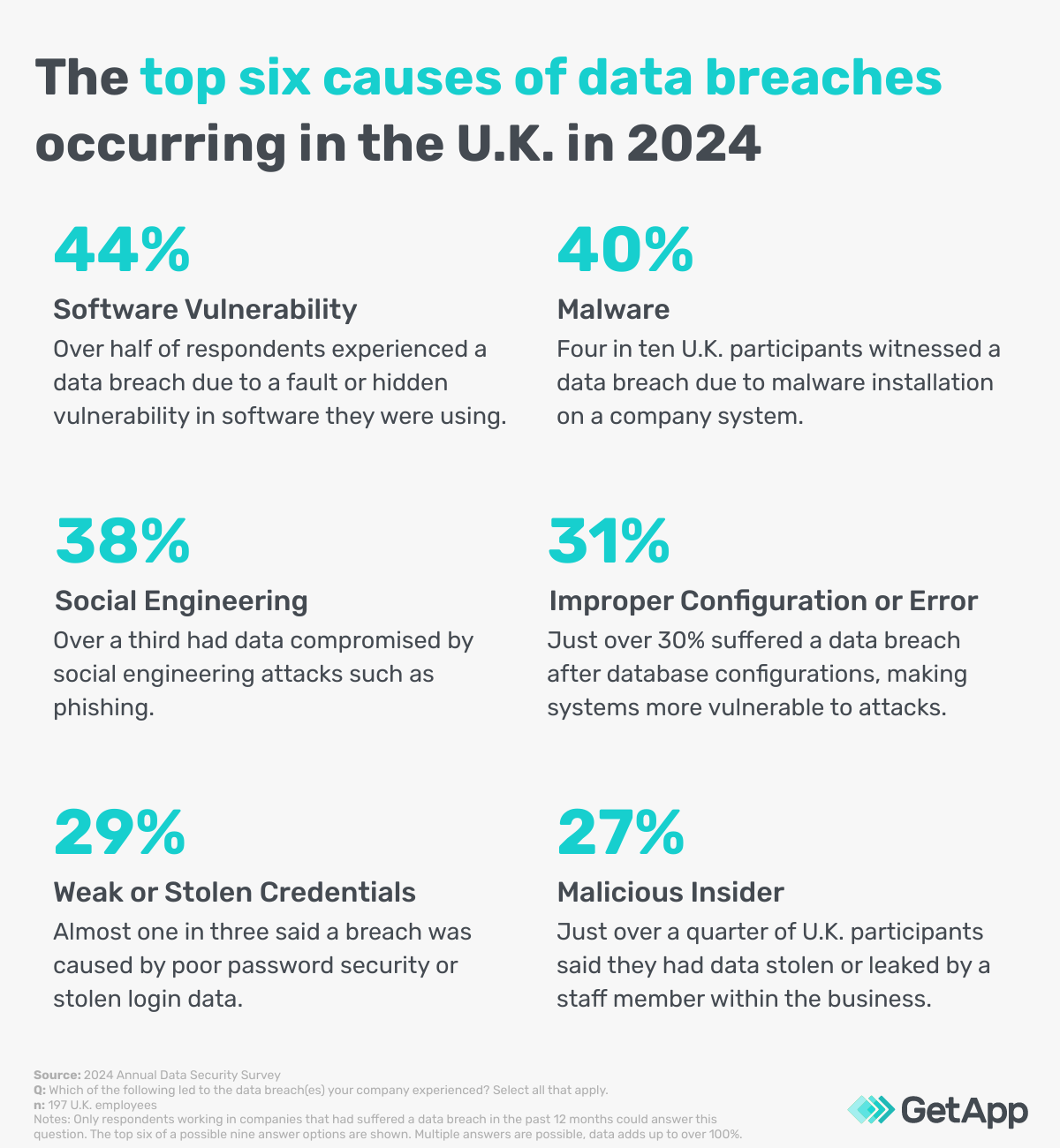
Why did 2025 become the year the security walls crumbled? Experts point to two primary drivers: the pervasive use of highly accessible Artificial Intelligence tools by threat actors, and persistent vulnerabilities in the global remote work structure that solidified post-pandemic.
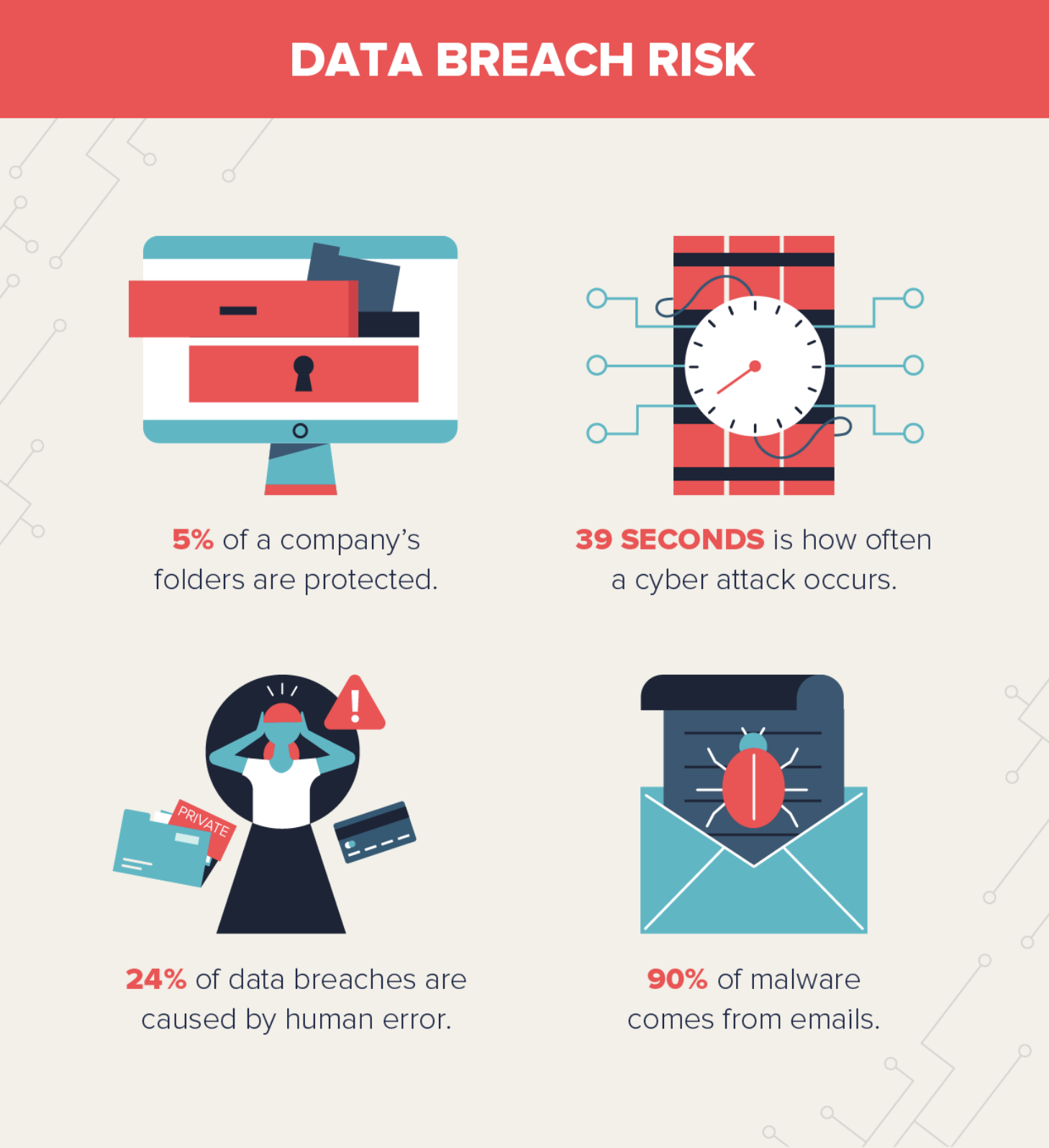
Cybercriminals are now leveraging generative AI to automate complex attacks. This means they can create millions of highly believable, contextually accurate phishing scams—known as spear phishing—in minutes. These AI-driven attacks easily bypass the basic filters that protected users just a few years ago. They are tailored to look exactly like communications from your actual bank, utility provider, or even your internal HR department.
Furthermore, the data collected in these breaches has become more valuable and complex. The trade of personal information on the dark web has become professionalized. Stolen data packets often include full sets of personally identifiable information (PII), ranging from social security numbers and biometric data to current addresses and employment history. This comprehensive data makes the victim ripe for full-scale identity theft.
- AI-Powered Sophistication: Increased ability to automate and personalize phishing and malware deployment, making attacks harder to spot.
- Supply Chain Weakness: Attacks often target third-party vendors with weak security, allowing criminals to jump from a small partner to a major corporation.
- Cloud Misconfigurations: Widespread reliance on cloud storage platforms often leads to accidental exposure of large databases due to human error in security settings.
The reality is that organizational security often lags behind the criminal innovation curve. This gap places the burden of protection squarely on the individual user. You must assume that at some point, one of the organizations holding your data will be breached. Your personal defense strategy must be built around mitigating the damage when that compromise occurs.
Essential Cyber Hygiene: Immediate Actions You Must Take Today
Securing your personal information requires immediate, decisive action. The following steps form the fundamental bedrock of personal cybersecurity and must be implemented without delay on all your digital accounts.
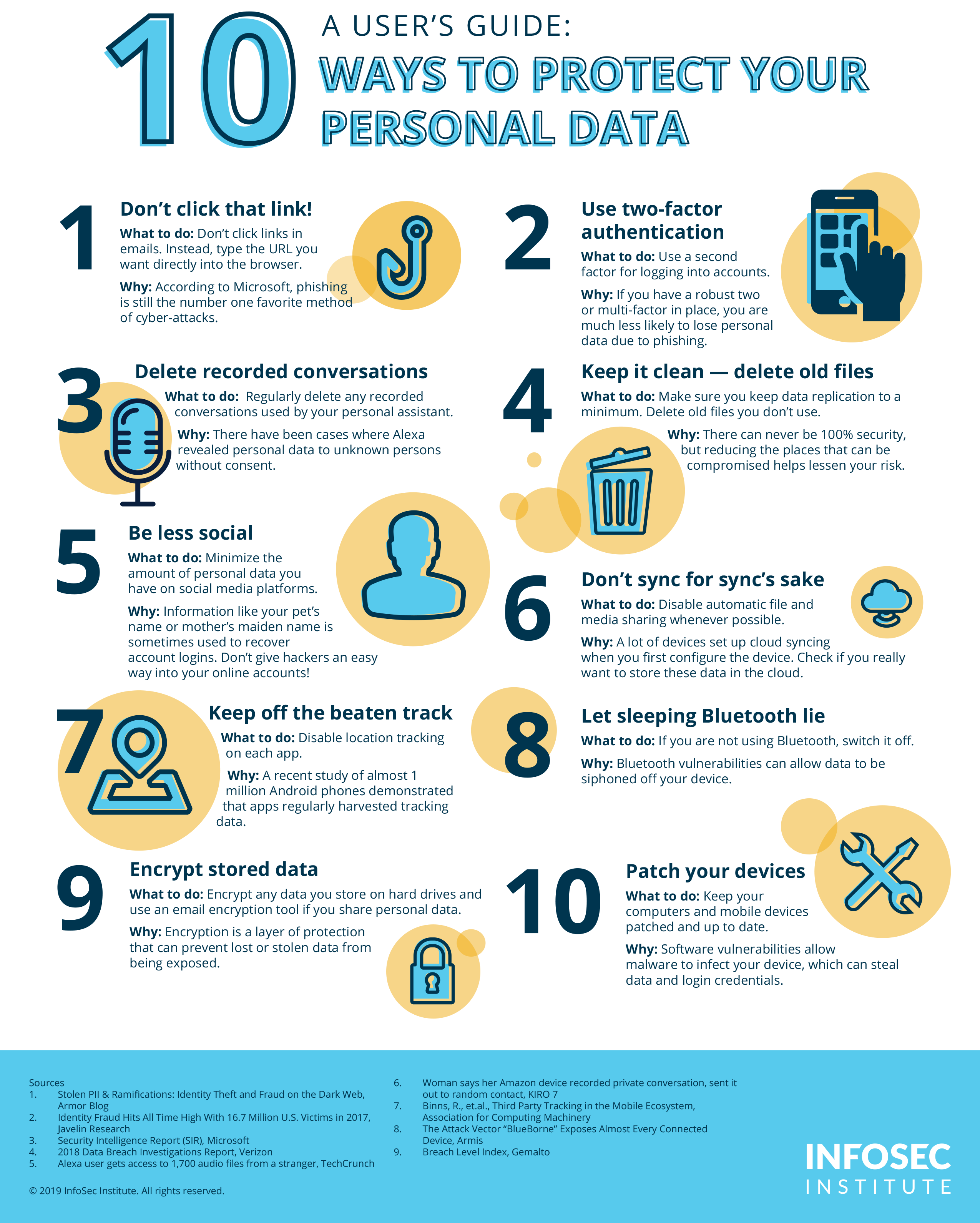
The single most powerful defense against unauthorized access, even if your password has been exposed in a breach, is Multi-Factor Authentication (MFA). MFA requires a secondary verification step—typically a code sent to your smartphone or a biometric scan—before login is approved. If you are not using MFA on your email, banking, and critical social media accounts, you are operating without a safety net.
Next, tackle the password problem. Password reuse remains a primary entry point for attackers using credential stuffing techniques (where stolen login data from one site is tested on hundreds of others). You must abandon the habit of recycling passwords. The solution is simple: adopt a dedicated password manager.
A reputable password manager service generates and securely stores long, complex, and unique passwords for every single service you use. This tool shields you from the catastrophic chain reaction that occurs when a single weak password leads to the compromise of your entire digital ecosystem.
- Activate Multi-Factor Authentication: Use authenticator apps (like Google Authenticator or Authy) over SMS text messages, as app-based MFA is harder for hackers to intercept.
- Adopt a Password Manager: Immediately replace all weak and reused passwords with unique, 20-character combinations.
- Prioritize Software Updates: Ensure your operating system, browser, and all major applications are set to update automatically. These updates frequently contain crucial security patches against zero-day exploits.
- Stay Skeptical of Phishing: Never click on unsolicited links or attachments, even if the sender looks familiar. Always manually navigate to the official website or use the verified app to check for legitimate notifications.
It is also vital to segment your digital activity. Consider setting up a secondary email address solely for retail newsletters, promotions, and non-essential services. This practice minimizes the risk that a low-stakes retail breach exposes the primary email address linked to your banking and financial records.
Advanced Defense Strategies for Proactive Digital Security
In the face of record-high breaches, relying only on passwords and MFA is insufficient. Proactive defense requires minimizing your digital footprint and actively monitoring for signs of compromise.
Protecting Your Financial Future: Credit Freezes and Monitoring
In the event that core PII, such as your social security number, is compromised, the clock starts ticking on potential financial identity theft. The most immediate and effective countermeasure is to freeze your credit reports with the three major credit bureaus (Equifax, Experian, and TransUnion). A credit freeze prevents any new accounts (credit cards, loans) from being opened in your name, rendering stolen SSNs practically useless to financial criminals.
Additionally, consider investing in a comprehensive identity theft protection service. These services specialize in dark web monitoring, continuously scanning known compromised data sets for your credentials. They provide alerts the moment your data appears in a breach, allowing you to change passwords and notify banks hours or even days before the compromised data is widely utilized.
The Power of Data Minimization
The best way to protect data is not to create it in the first place. Practice strict data minimization. Be highly selective about the information you share online. If a website asks for details that are irrelevant to the core service—such as your full birthday or home address on a forum—do not provide it.
Periodically engage in "digital decluttering." Review your old accounts and services. Do you still have profiles on forums, mailing lists, or outdated social media sites you haven't touched in five years? Each dormant account is an unsecured point of risk. Delete them permanently. Fewer accounts mean fewer targets for cybercriminals.
- Utilize a High-Quality VPN: Use a reputable Virtual Private Network, especially when using public Wi-Fi or when traveling. A VPN encrypts your traffic, making it impossible for third parties to intercept your data transmissions.
- Review Permissions: Regularly audit the permissions granted to third-party applications on your smartphone and cloud services. Restrict apps from accessing your contacts, camera, or location unless absolutely essential for functionality.
- Physical Security Keys: For extremely high-value accounts (e.g., administrator accounts, cryptocurrency exchanges), upgrade security by using FIDO2-compliant hardware security keys (like YubiKey or Titan).
- Enable Privacy Browsing: Utilize privacy-focused browsers or extensions that block trackers and excessive web fingerprinting, reducing the amount of behavioral data available to advertisers and potential threat actors.
The record-setting data breaches of 2025 serve as a permanent warning: the perimeter has collapsed. Personal security is an ongoing, active responsibility. By implementing strong Multi-Factor Authentication, utilizing powerful password managers, and adopting proactive defense strategies like credit freezing and data minimization, you create a robust shield that helps ensure your personal information remains safe even when the large organizations holding your data inevitably fail.
Vigilance is your greatest weapon in the fight against cybercrime. Stay informed, and stay secure.
Data breaches climbed to a record high in 2025. How to protect your personal information
Data breaches climbed to a record high in 2025. How to protect your personal information Wallpapers
Collection of data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for your desktop and mobile devices.
Vibrant Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Desktop
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Stunning Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture for Desktop
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Dynamic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Photography
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Artistic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture in 4K
Find inspiration with this unique data breaches climbed to a record high in 2025. how to protect your personal information illustration, crafted to provide a fresh look for your background.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View in 4K
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Wallpaper in HD
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Detailed Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Photo Collection
Explore this high-quality data breaches climbed to a record high in 2025. how to protect your personal information image, perfect for enhancing your desktop or mobile wallpaper.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Collection
Immerse yourself in the stunning details of this beautiful data breaches climbed to a record high in 2025. how to protect your personal information wallpaper, designed for a captivating visual experience.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Scene Collection
Discover an amazing data breaches climbed to a record high in 2025. how to protect your personal information background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment for Desktop
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Nature
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View Photography
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Photography
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Picture Nature
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.

Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Beautiful Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Digital Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Your Screen
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.
Download these data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for free and use them on your desktop or mobile devices.
0 Response to "Data breaches climbed to a record high in 2025. How to protect your personal information"
Post a Comment